How to Surf the Internet Anonymously and Leave No Evidence
- June 27, 2016
- 0
by Olav Phillips
 Over the last few years, and as Government surveillance has expanded, more and more people are looking for ways to control their internet footprint. Especially now with the revelations of Google listening to your life through your microphone or the revelations about internet surveillance. That added to the very real browser tracking corporations are performing against you every time you visit their site makes for a situation where you, an individual, are being data mined, categorized, and your behaviors tracked and indexed. In fact in a widely publicized case, the retailer Target actually figured out a teenage girl was pregnant before her father knew! On the simpler end, website owners store logs with IP Addresses (unique address identifiers which are assigned to you when you start your DSL/Cable modem) and log what you do at a website.
Over the last few years, and as Government surveillance has expanded, more and more people are looking for ways to control their internet footprint. Especially now with the revelations of Google listening to your life through your microphone or the revelations about internet surveillance. That added to the very real browser tracking corporations are performing against you every time you visit their site makes for a situation where you, an individual, are being data mined, categorized, and your behaviors tracked and indexed. In fact in a widely publicized case, the retailer Target actually figured out a teenage girl was pregnant before her father knew! On the simpler end, website owners store logs with IP Addresses (unique address identifiers which are assigned to you when you start your DSL/Cable modem) and log what you do at a website.
This was the first phase – Do Nothing, Total Ignorance.
 Ok so the Government and Corporations are watching you, so what do you do? How do you prevent this data mining and behavioral classification? The answer is surprisingly simple – you secure it and randomize it. Now I know what you are thinking… That sounds tough and really technical, but the truth is that it’s not. It turns out as Governments and Corporations have expanded their surveillance people have responded and found new ways to protect their identities, interests, and habits.
Ok so the Government and Corporations are watching you, so what do you do? How do you prevent this data mining and behavioral classification? The answer is surprisingly simple – you secure it and randomize it. Now I know what you are thinking… That sounds tough and really technical, but the truth is that it’s not. It turns out as Governments and Corporations have expanded their surveillance people have responded and found new ways to protect their identities, interests, and habits.
The Second Phase – The Anonymizer…
The second phase really came into prominence after the Patriot Act was signed in 2001. Sites like the Anonymizer came into the forefront. These sites allowed you to use a web page to load other web pages. Eventually, these service became proxies where instead of having to load a web page to load another web page the user would pass all pages through their service.
But there were several issues with this:
- The connection between the computer and the proxy is not necessarily secure unless protected by HTTPS/SSL.
- Normally proxy providers keep access logs and activity logs.
- Proxy site generally have less distributed egress points making it easier to find the source.
- Proxying traffic can cause confusion when you connect to a friends or work connection.
- Proxying does not protect you from hackers or people intent on directly accessing your computer.
Ok, it’s sounding pretty bleak. You have large numbers of people, including startups funded by the CIA who are socially mapping you. You have corporations who are tracking you, analyzing you, and categorizing you all through your internet connection so what do you do?
The Third Phase – GO GET A VPN!
 So now we have seen the problem but how do you protect yourself from all this? The answer is a VPN Service.
So now we have seen the problem but how do you protect yourself from all this? The answer is a VPN Service.
So what is a VPN??? Basically, a Virtual Private Network, or VPN, is a bunch of users / computers networked together over a public network like the internet and connected securely. In business – VPNs are used to connect remote facilities or offices, and remote workers use VPNs to access to resources when they’re not physically in the office, or as a way for securing and encrypting communications when people are using a public network.
 Here is the important part – When you go to connect to a VPN or VPN service, you the launch a VPN client on your computer, once both computers have verified each other as authentic, all of your internet communication is encrypted and secured from eavesdropping. Remember that is ALL communication from your computer to the internet and back! This include DNS requests!
Here is the important part – When you go to connect to a VPN or VPN service, you the launch a VPN client on your computer, once both computers have verified each other as authentic, all of your internet communication is encrypted and secured from eavesdropping. Remember that is ALL communication from your computer to the internet and back! This include DNS requests!
There are also other reasons why using a VPN Service is a great idea when you are surfing the internet:
- Location Control – You can control where you appear to come from. So when you visit a website they will think you are coming from Canada, Iceland, or maybe Japan. So no one knows where you are from!
- Encrypted Connections – Communicate with the internet using encryption with anonymous email, hidden IP addresses and an extreme level of privacy.
- Privacy Enabled – No one can monitor, intercept, throttle, or buffer your internet communications or online activity. Become completely anonymous…
- Connect Anywhere – These services work with Windows, MAC, Linux, iPhone, iPad, Android, Windows Mobile. Secure connections anywhere with total protection.
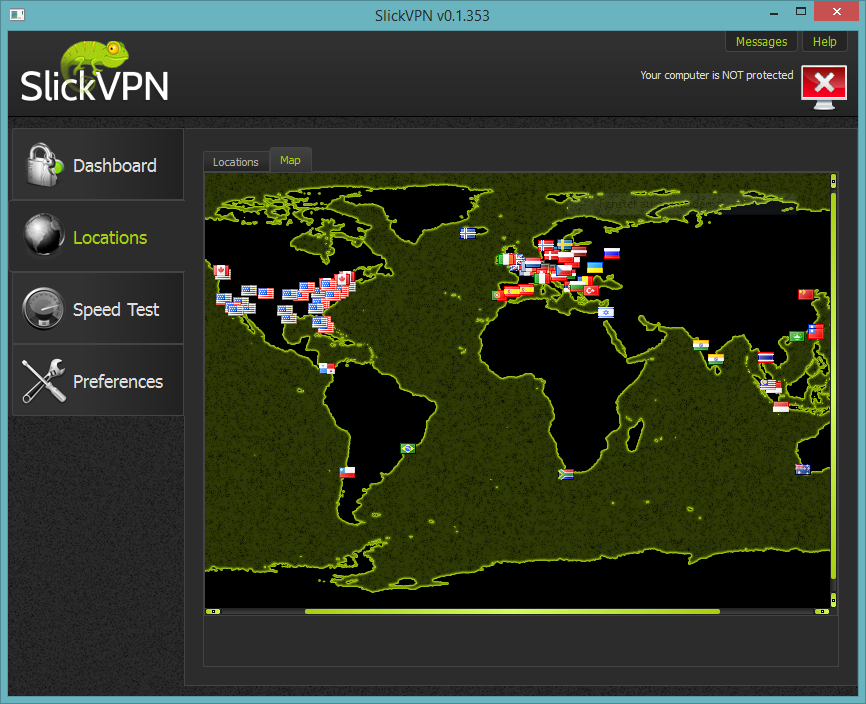
No matter what the reason – securing your internet browsing and connection is critical as we move forward on the internet of things. Monitoring is rampant and you need to protect your identity! There are a number of services which provide this service and most are relatively cheap. At PARANOIA we use SlickVPN which has servers in over 125 gateways in over 45 countries and only costs $4/month! Check them out by clicking the logo below.